Modernizing Security Operations with Microsoft Sentinel: A Comprehensive Guide
Introduction
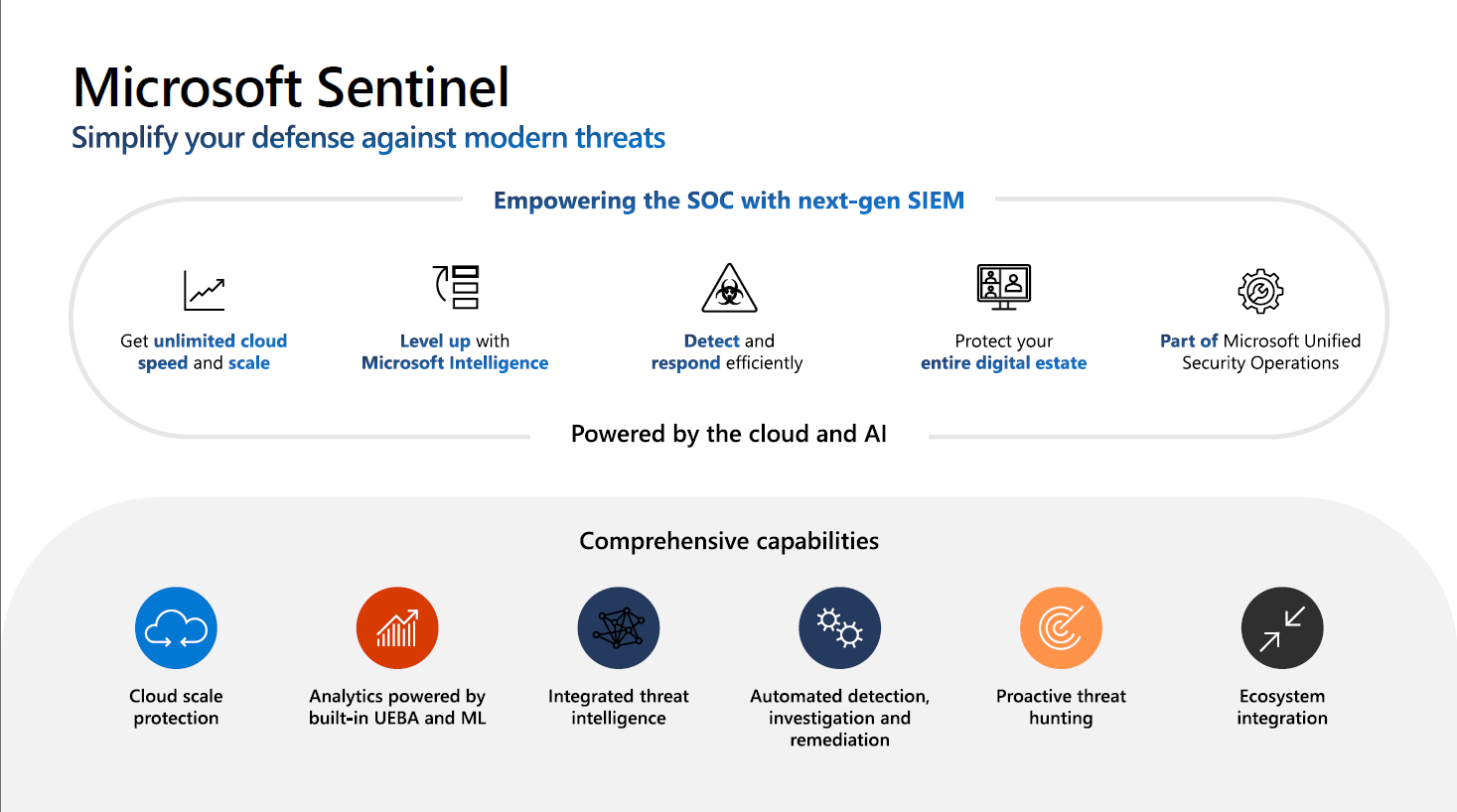
As cyber threats evolve, organizations need robust Security Operations Center (SOC) capabilities. Microsoft Sentinel offers a next-generation Security Information and Event Management (SIEM) solution that combines the power of cloud scalability with advanced AI capabilities.
Microsoft's Unified Security Operations Platform
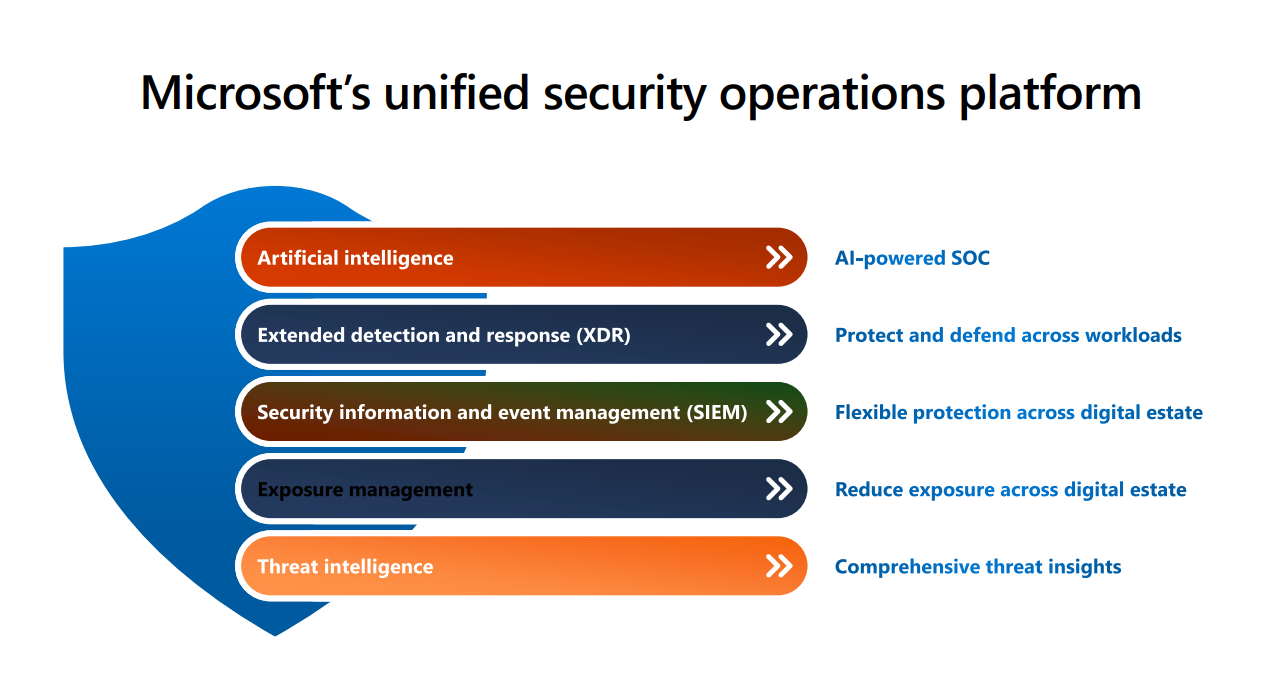
Microsoft's unified security operations platform consists of five key layers:
-
Artificial Intelligence (AI-powered SOC)
- Advanced analytics and automation
- Machine learning-based detection
- Intelligent threat hunting
-
Extended Detection and Response (XDR)
- Protect and defend across workloads
- Cross-platform visibility
- Automated response capabilities
-
Security Information and Event Management (SIEM)
- Flexible protection across digital estate
- Centralized log management
- Advanced correlation capabilities
-
Exposure Management
- Reduce exposure across digital estate
- Vulnerability assessment
- Risk-based prioritization
-
Threat Intelligence
- Comprehensive threat insights
- Real-time threat feeds
- Automated indicator sharing
Key Components of Modern SecOps
Microsoft Sentinel Core Capabilities
-
Cloud-Scale Protection
- Unlimited cloud speed and scale
- Comprehensive coverage across on-premises and multi-cloud environments
- Protection for IT, OT, and IoT assets
-
AI-Powered Analytics
- Built-in User and Entity Behavior Analytics (UEBA)
- Machine Learning-based threat detection
- Automated investigation and response capabilities
-
Threat Intelligence Integration
- Real-time threat intelligence feeds
- Custom indicator management
- Automated threat response workflows
SOC Optimization Strategies
Cost Management
- Data Tiering
- Analytics logs for high-value security data
- Basic logs for investigation and automation
- NEW: Auxiliary logs for verbose, low-cost storage
- Summary rules for optimized data aggregation
Coverage Optimization
- Threat-based recommendations
- Automated discovery of environment
- Continuous security posture assessment
- Integration with Microsoft Defender XDR
Efficiency Improvements
- Copilot for Security integration
- Automated incident response
- Machine learning-powered analytics
- Streamlined workflow management
The Unified Security Operations Platform
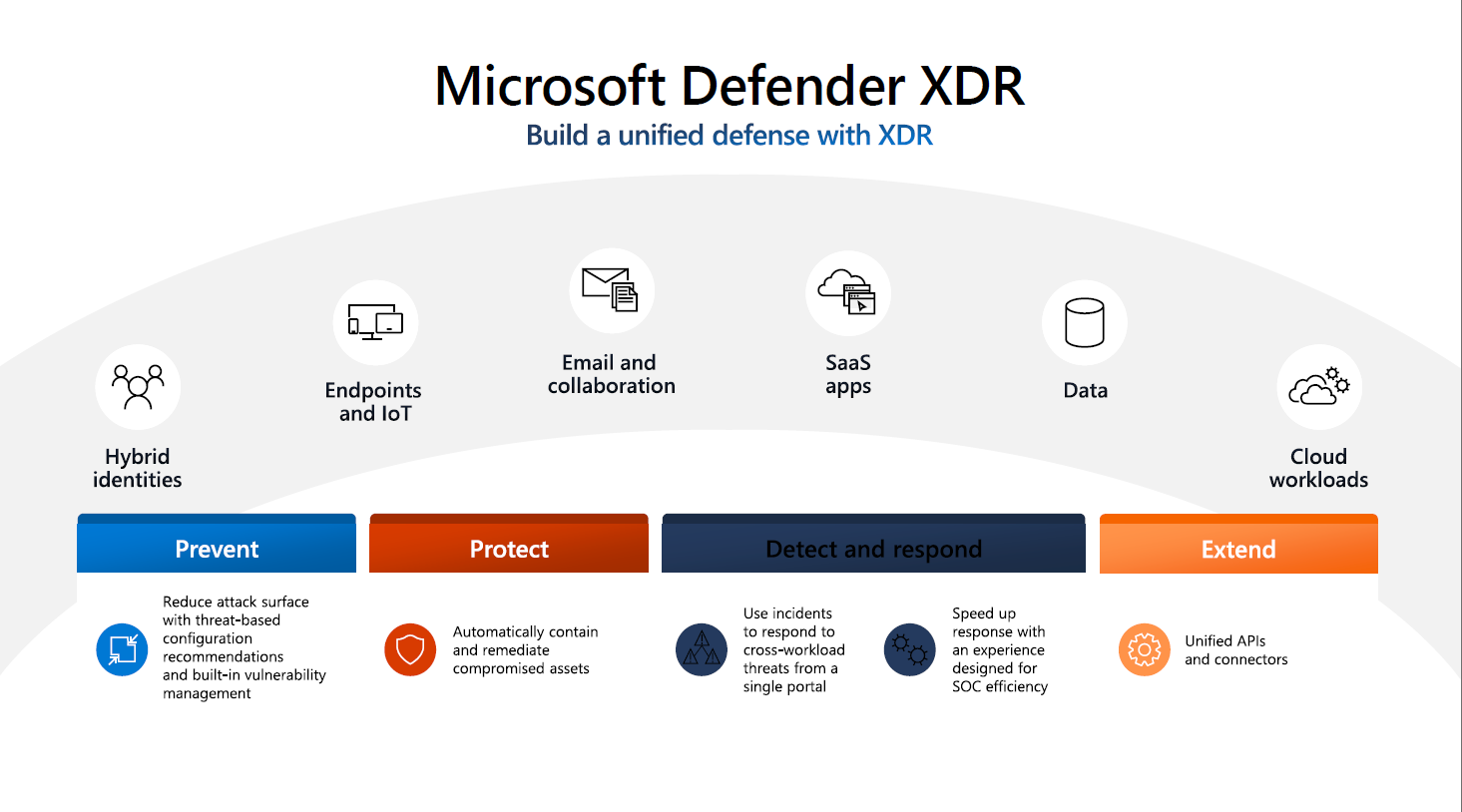
SIEM + XDR Integration
-
Enhanced Detection
- Cross-platform threat visibility
- Automated correlation
- Advanced hunting capabilities
-
Streamlined Response
- Unified incident management
- Automated remediation
- Cross-platform orchestration
-
Comprehensive Protection
- Identity and access management
- Endpoint security
- Cloud workload protection
Implementation Best Practices
Planning Phase
- Assess current security posture
- Define security requirements
- Plan data collection strategy
- Design workspace architecture
Deployment Phase
- Configure data connectors
- Implement detection rules
- Set up automation workflows
- Enable continuous monitoring
Optimization Phase
- Regular security assessments
- Cost optimization reviews
- Coverage gap analysis
- Performance tuning
Microsoft Sentinel Components
Data Collection
-
Data Connectors
- Microsoft 365 Defender
- Azure AD
- Azure Activity
- Cloud App Security
- Third-party sources
-
Log Analytics Workspace
- Data retention settings
- Access control
- Query performance
Analytics
-
Built-in Rules
- Microsoft security analytics
- Threat intelligence alerts
- Anomaly detection
-
Custom Rules
- KQL-based detections
- ML Behavior Analytics
- Scheduled queries
Investigation
-
Incident Management
- Automated creation
- MITRE ATT&CK mapping
- Severity classification
- Assignment and tracking
-
Investigation Tools
- Interactive investigation graph
- Entity behavior analytics
- Timeline analysis
Response
-
Automation Rules
- Incident triggering
- Automated enrichment
- Response orchestration
-
Playbooks
- Logic Apps integration
- Custom workflows
- Third-party integration
Hunting
-
Query Templates
- Built-in hunting queries
- Custom hunting
- Bookmarks and sharing
-
Notebooks
- Jupyter integration
- Python analysis
- Visualization tools
Conclusion
Modern security operations require a comprehensive approach that combines advanced SIEM capabilities with XDR integration. Microsoft Sentinel provides the foundation for building a robust security operations center that can effectively detect, investigate, and respond to modern threats while optimizing costs and improving operational efficiency.
This post is based on Microsoft Security Partner training materials and represents current best practices in modern security operations.